How to protect your digital assets from fire, flood, phishing, forgetfulness, and other forces of nature.
There’s a “cold room” in Attinghausen, Switzerland — it’s lined with slabs of steel, and it sits some 300 meters down inside a granite mountain in an old, repurposed military bunker. What’s inside? Air gapped hardware with the private keys of high value crypto holders who are looking for a little peace of mind.
These security measures might sound extreme, but the attack vectors are many in the cryptosphere: shams, scams, extortion, friends turning on friends, spoof friends. Users can’t flag fake accounts fast enough:
Fake Vitaliks. Fake Joe Lubins. How hard does anyone really look at social media handles? Someone flying through twitter is prone to miss the “l” in @etlhereumJoseph.
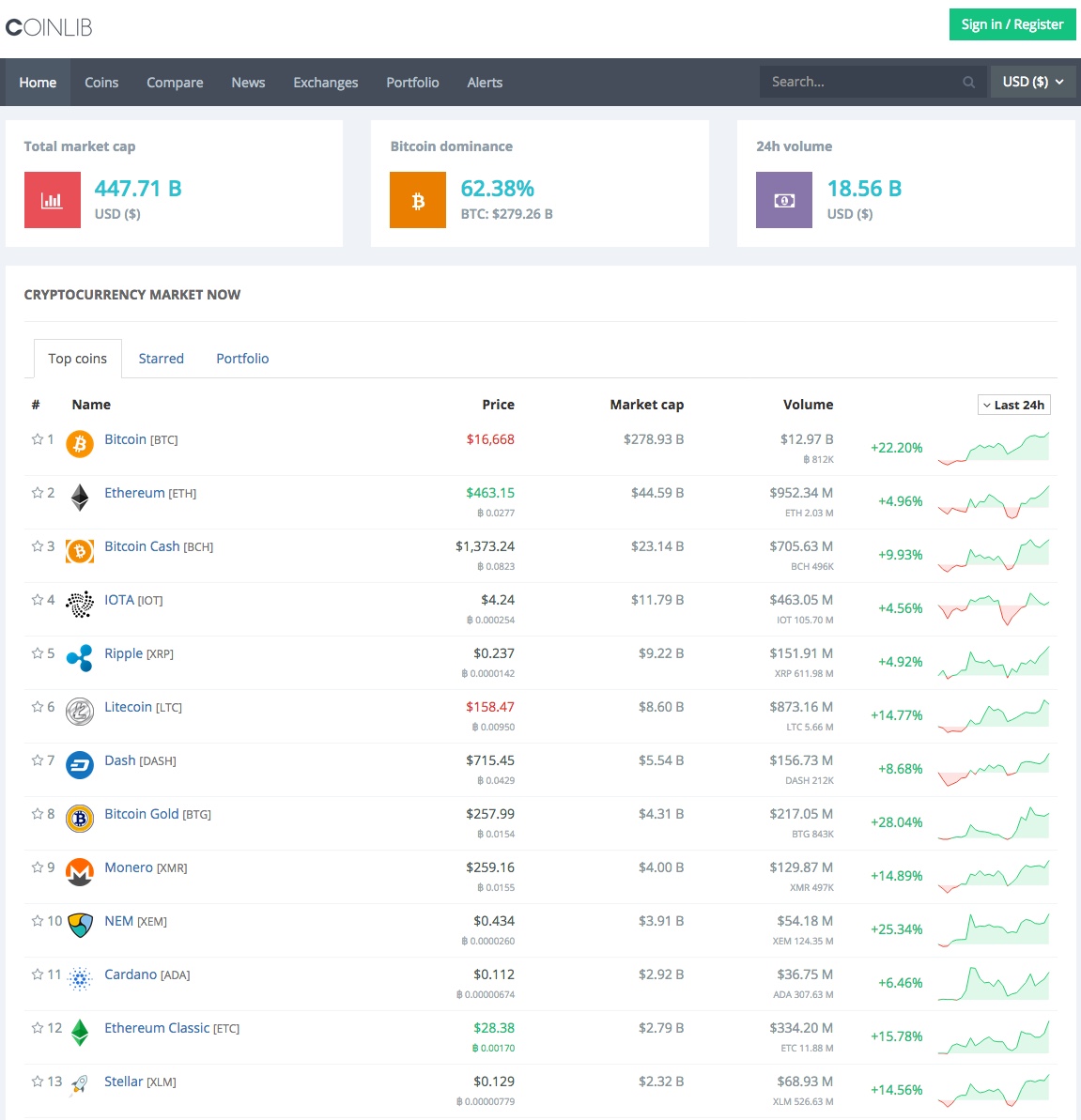
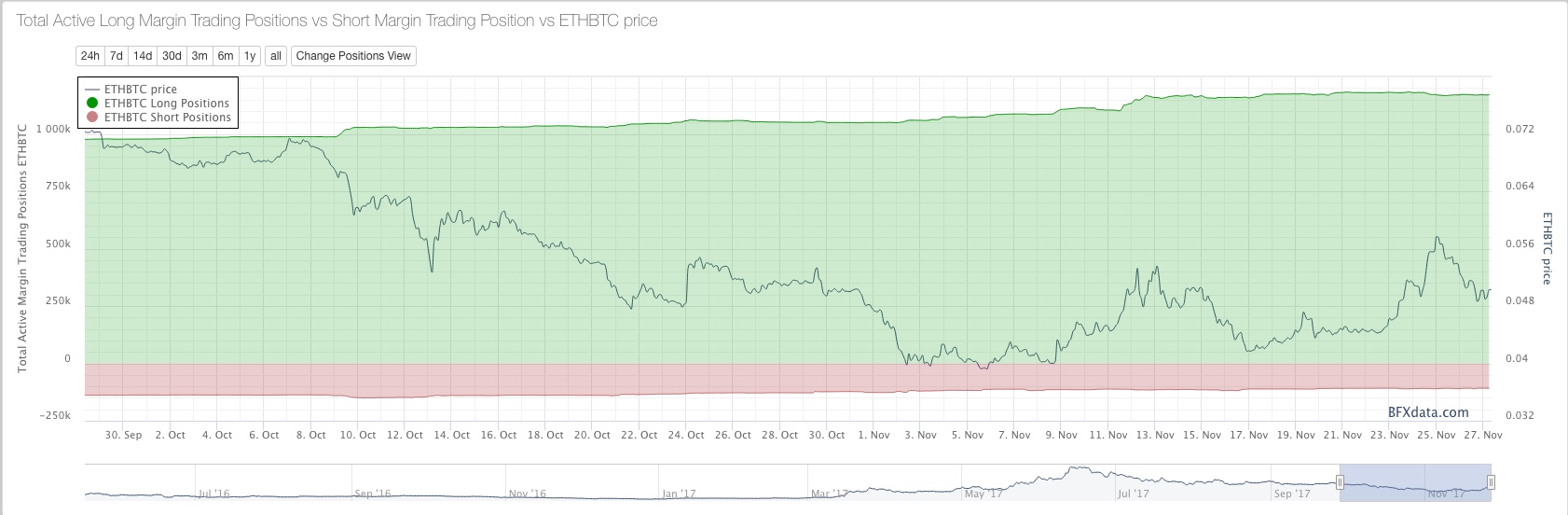
For many users, the bulk of their crypto is still sitting “hot” — in online wallets on centralized exchanges, which have had their share of reckonings over the years: the infamous Mt. Gox hack in 2014, in which hackers made out with approximately 740,000 BTC, and the Bitfinex breach more recently, which drained almost 120,000 BTC from the exchange.
And then of course the age-old threats, fire and forgetfulness (one man accidentally threw out $9 million worth of bitcoin). Attack vectors can be unassuming, furry even:
The problem is, misplaced crypto has a way of altogether disappearing — sometimes across jurisdictions and beyond the reach of the law, sometimes into cryptographic black holes (in 2011, 2,609 BTC vanished on Mt. Gox because of a scripting error). What’s liberating about blockchain is that you can become your own bank. But that can also be a daunting thing for many of us who have grown comfortable letting central institutions manage our lives for us. It’s time we educate ourselves.
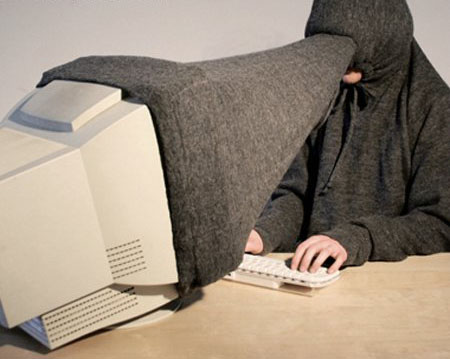
Thankfully, Nick Dodson, founder of BoardRoom (now GovernX), just published his GitBook, “Pro Tips for Ethereum Wallet Management,” a security manual for naifs and tin foil hat types alike. Dodson’s personal security measures are admittedly Snowden-grade — we’re talking blanket over the screen and everything — but his mission is to empower users, not scare them off. He acknowledges the tradeoff between convenience and security. Too many security layers and you end up stumping even yourself when trying to access your crypto. Dodson gives you the resources to decide for yourself how sophisticated you want to get.
A word of caution: Compiling these pro tips brings with it the meta-anxiety that any tools or security measures we recommend here will now become the focus of bad actors. So stay sharp. But stay with it. Blockchain isn’t just about surviving. It’s about creating choices for yourself. As Dodson writes, “Be vigilant and you will thrive.”
1. Know the attack vectors.
AKA Know your enemy. Watch out for the proverbial “man in the middle” — someone trying to get in between you and your destination. Spoof sites, malicious websites that mimic other sites, can be picture-perfect nowadays. Make sure you double check URLs. Better yet, bookmark your crypto sites, and stick to your bookmarks (MetaMask also blacklists MyEtherWallet clones for you). Verify software downloads. A copy of Tails OS is no good if it’s infested with spyware. A man-in-the-middle attack can even be literal: one guy lost his life savings to a reseller on Ebay who pulled the recovery seed from a hardware wallet and repackaged the wallet. Always buy your hardware wallet directly from the manufacturer. Now think two steps ahead. Maybe your URLs look good. But how do you know someone hasn’t hacked your Wi-Fi, spoofed the DNS, and redirected you to different IPs? Safe computing is like chess: always assume your opponent is smarter than you.
2. Generate strong passwords.
You should know the drill by now — no birthdays, street addresses, song lyrics, etc. (don’t even get me started on my mom’s passwords). But even if you mash the keys on your keyboard, that’s still not random enough (you are not a good source of entropy). Password-crackers can rifle through 350 billion guesses per second. Use a random mnemonic generator to create a passphrase, or buy a hardware wallet to generate powerful keys and signatures for you. Multiple passwords are better than one. Multi-signature wallets, like Gnosis’, require multiple keys to validate transactions. And use two-factor authentication for everything: email, exchanges, Steam, etc. Heads up: the countdown might be annoying, but app-based two-factor is much more secure than SMS. Let this be your warning.
3. Use cold storage.
You don’t have to go 300 meters underground, but you should keep the majority of your crypto “cold” — that is, air gapped and offline. Only keep an amount in exchanges and online wallets that you are willing to lose. You can either build an air gapped computer by removing the network card from your PC or laptop (Tails is an operating system that you can run offline), or buy a hardware wallet. When generating the seed phrase, plug your hardware wallet into a wall outlet to keep it as cold as possible. Paranoia tips: cover the mic/camera of your laptop and remove any electronic devices from the room.
4. Test everything.
Make small test transactions or practice with a tiny bit of funds on a test network before going full monty. Never manually type out addresses (over 9000 ETH have been lost forever due to typos). Copy and paste, use Ethereum Name Service, or scan QR codes. Make sure your scan app is secure (Pro Tip #1: Know the attack vectors). Double-check the identicon of your target address. Before transferring any crypto onto your hardware wallet, test your seed phrase. If you’re building an air gapped computer, record and re-check the MD5 checksum before and after you load data onto the SD card. For the love of Ethereum, test everything.

5. Store your seed phrase(s) across different devices and locations.
A standard Bip39 seed phrase is that curious string of 24 words from which you can derive a private key. Manage your seed with utmost care. If you write it down on paper, consider making two copies and storing them in separate locations. SD cards are another storage option, but they rarely last more than five years, and they could be wiped by a pinch (EMP bomb). Use both analog and digital just in case (some people hammer their seed phrases into steel). If you want to level up: store pieces of your seed phrase in separate, safe locations. And remember: meticulously record your steps, so you (or your heirs) can recreate the seed.
6. Maintain plausible deniability.
Plausible deniability in the cryptoverse means the ability to keep certain data hidden. Here’s a helpful public emission guideline: don’t broadcast your holdings, and especially don’t tell the world (over social media) the exchanges where you keep all your crypto (again, this guy). All your crypto shouldn’t be hot anyway (Pro Tip #3: Use cold storage). You can hide accounts under different HD paths on your hardware wallet in case someone comes knocking. Also, minimize your risk exposure by distributing your holdings across multiple wallets.
7. Level up. Help the ecosystem.
Dodson finishes his GitBook by recommending four different levels of wallet setup, Level 4 being for the most rigorous users. It’s your call how sophisticated you want to get. But remember: your security choices affect not only you but the ecosystem. If you don’t use two-factor authentication, and someone seizes your email (that, say, you left open on a library computer), when that bad actor starts phishing your personal network, that’s on you. So challenge yourself to level up. Experiment with hardware wallets, Tails, and multi-sig. Channel your inner Snowden. Learn by teaching. Tell your friends about cold storage, and your mom about strong passwords. Help the community flag spoof sites and fake accounts. Dodson’s “Pro Tips” are a gift to the ecosystem, and something we can pay forward.
Source: https://media.consensys.net