Roundup #6
Posted on .
Posted on .
Blockchains are beginning to turn green. This post describes some of the IC3 research in this direction.
The glorious view from our windows at Cornell Tech takes in 432 Park Avenue, the tallest residential building in the world. This tower is a monument to many things. Above all, for a student of Financial systems, it epitomizes ways to store wealth with breathtaking waste. (Fittingly, it was inspired by a wastepaper basket, shown to the right.) Buildings like it are sprouting up around NYC as investment vehicles for the ultra-wealthy, and their owners don’t actually live much in them. 432 Park and its ilk are essentially hollow vaults.
Something similar can be said for Bitcoin. As a concept and technological inspiration, Bitcoin is a marvelous thing. And unquestionably like 432 Park, it does see legitimate and valuable uses (and some shady ones). As a currency, though, Bitcoin serves in no small degree as a wasteful and ecologically damaging way for people to park their money.
There are a number of ways to substantiate this claim. One is in terms of its electricity consumption. Estimates vary, but it is likely that the Bitcoin network consumes roughly as much electricity as a nuclear reactor, about 1/3 of the entire electricity consumption of the entire country of Ireland. (See our back-of-the-envelope calculations in the blog notes.) To view this in another light, a recent IC3 paper estimated the cost-per-confirmed transaction at as much as $6.20 in capital costs and electricity. (Transaction rates have been rising, and today the figure is substantially lower, but still high.) That’s $6.20 in resources per transaction to move money between accounts in the same system.
Bitcoin proponents argue that this is simply the cost of decentralization. A credit-card network doesn’t provide the pseudonymity, freedom from government interference, portability, and other features of Bitcoin, so it isn’t comparable. This is true. But it isn’t a law of nature that a system like Bitcoin should be so resource-intensive. Researchers at IC3 believe that the many benefits of Bitcoin can be had without the waste. In a few papers released over the past month or so, we’ve outlined three different approaches to the development of greener alternatives:

If we can’t reduce waste at the source, why not recycle? That’s the premise of the first, and simplest idea, called PieceWork. Piecework involves a slight modification to the standard Proof-of-Work (PoW) construction, decomposing it into two layers. One layer produces small PoWs called puzzlets that play a critical role in the mining process and can also, as we shall show, serve useful non-mining purposes.
Consider a standard cryptocurrency, abstracting away into a single value X the details of what gets hashed into a PoW (transactions, the previous block, etc.). A miner’s task then is is simply to search for an input (“nonce”) n∈N for which
H(X, n) ≤ Z,
where Z is a threshold representing the difficulty of the PoW.
To decompose a PoW into two layers, we instead construct it as follows:
H(X, n) = Fout (X, Fin (X, n; rin ), rout ),
where rin = H0(r) and rout = H1(r) for distinct hash functions H0, H1 and a secret value r. (These two values are a technical requirement to prevent what are called block withholding attacks. See the blog notes.)
A valid solution is a value n such that
Fin (∙, n, ∙) < Zin and Fout (∙, n, ∙) < Zout.
To solve this puzzle or PoW, a miner must first find an n such that Fin (∙, n, ∙) < Zin. This inner-puzzle is what we call a puzzlet. To solve the whole PoW, a miner must find a puzzlet solution. The puzzlet solution must additionally satisfy Fout (… n…) < Zout, meaning that a miner must in general come up with many puzzlet solutions to solve the PoW as a whole. By setting Zin + Zout = Z, one obtains a PoW with the same difficulty as that in (1).
What’s the benefit of this two-layered structure? A puzzlet, i.e., the task of finding a solution n to Fin (∙, n ,∙) < Zin, can be outsourced by a miner or mining pool operator to a worker, and put to any of several non-cryptocurrency goals. DoS prevention for TLS is one example. TLS requires computationally intensive crypto operations from a server to set up connections. Thus it’s a natural target for DoS attacks, prompting the idea of requiring clients to solve PoWs if a server comes under attack, an idea now floated in an IETF proposal. These PoWs used for DoS mitigation can themselves be puzzlets. The effect is that the server becomes a mining pool operator, and its clients become workers. And a DoS attacker effectively showers the victim HTTPS server with cryptocurrency. (Of course, a server can also dispense puzzlets and make money even when it’s not under attack…) Other examples of puzzlet uses are spam prevention (the original PoW goal proposed by Dwork and Naor), MicroMint, and Tor relay payments.
In summary, PieceWork requires only a small modification to standard cryptocurrency PoWs. It turns them into dual-use computational problems and recycle wasted mining effort. How much recycling it can feasibly accomplish is an open research question. PieceWork benefits from a number of previous, related ideas. Our short paper on it can be found here. PieceWork will be presented in April at BITCOIN 2017.

A very different approach to minimizing waste is embraced in our second project, a system called REM. Rather than relying on hash-based PoWs, it makes use of an entirely different type of PoW, in which the W, i.e., the work, is useful. We call this concept Proof of Useful Work (PoUW).
Of course, traditional PoWs have several useful properties, prime among them the ease with which solutions can be verified. Most workloads don’t have this property. To enable verification of work on arbitrary useful workloads, REM relies on a new technology: Intel SGX.
Intel’s new SGX (Software Guard eXtensions) trusted execution environment technology. In a nutshell, SGX enables the execution of an application in a hardware-protected environment, called an enclave, that is isolated from the operating system and other applications. It thus protects the application against tampering by even the owner of the machine on which it’s running. SGX also enables generation of an attestation that proves to a remote party that a particular application was running in an enclave. SGX is already supported in many recent-model Intel CPUs.
As a good way to see how SGX can facilitate mining, it’s worth discussing an elegant mining scheme proposed by Intel called PoET (Proof of Elapsed Time). The idea behind PoET is simple. If miners use SGX, then they can be forced to use only a sanctioned piece of mining software that simulates PoWs. Standard PoWs have solution times that are exponentially distributed. A PoET client can thus sample a solution time from an exponential distribution, simply sit idle until this time elapses, and then wake up with a block in hand. The first client to awake gets to publish its block. An SGX attestation proves to others in the system that the client idled as it should have.
PoET has several nice features. Foremost among them is the fact that (at first glance) it’s virtually energy-waste-free. Clients idle instead of hashing. Block solution times can be tuned to mimic those of a standard mining regime, like Bitcoin or Ethereum mining. Thus PoET can effectively be plugged into such schemes. It is also relatively egalitarian in that it achieves precisely one vote per CPU. PoET, though, has two technical challenges. We call these the broken chips and stale chips problems.
First, the broken chips problem. SGX security is imperfect and, as with any trusted hardware, it’s to be expected that a well-resourced adversary can break it. Thus, it’s to be expected that some SGX CPUs will be broken. In the basic PoET scheme, a broken chip has devastating effect, as it enables a miner to simulate a zero mining times and win every consensus round, i.e., publish all blocks. Intel has proposed a statistical testing regime to detect breaks, but details aren’t published and formal foundations are needed for a good analysis.
REM faces the same challenge. In REM, we have developed a rigorous statistical testing regime with formal foundations and shown analytically and empirically that it is highly effective: It can strictly limit the gains of adversaries that have broken chips while minimizing incorrect rejection of blocks from honest miners.
The stale chips problem is more subtle. Our economic analysis shows that in many practical settings in PoET and related systems, it will be advantageous for a miner to buy old (“stale”) SGX CPUs and cobble them together into “farms” that mine cheaply. Such farms reinstate a fraction of the waste that PoET is trying to avoid to begin with. This is where REM’s Proof of Useful Work (PoUW) approach comes into play. In a nutshell, with PoUW, miners run whatever workloads they consider to be useful—protein-folding computations and ML classification algorithms are a couple of examples considered in our work. Miners can prove that they did work on these problems using SGX. The probability of a miner mining a block is proportional to the amount of work she does. Thus, REM turns otherwise useful work into mining effort. Making PoUW work is technically challenging. It requires that workloads be themselves compiled and instrumented using SGX to prove correctness, an innovation of independent interest introduced in REM.
The biggest objection lodged against SGX-based mining is the fact that it places Intel in charge, undermining the decentralization at the heart of permissionless ledgers. Of course, Intel is already a trust anchor. But we’d view this another way, and characterize REM and PoET as partially decentralized. You can read about REM here, in a paper under submission.

Our final approach to reducing cryptocurrency waste is one both proposed and studied by many projects in the cryptocurrency community since the inception of Bitcoin. This idea is called proof of stake, and revolves around the basic premise that rather than mining simulating a lottery where your chance of finding a block is proportional to computing power, mining simulates a lottery where your chance of finding a block is proportional to the number of coins (or “stake”) you have in the system.
A key roadblock to the adoption and deployment of proof of stake systems involves questions around the security guarantees that they provide. This continues to be an ongoing source of controversy and debate in the community, with sources like the Bitcoin Wiki claiming that “Proof of Stake alone is considered to an unworkable consensus mechanism” and efforts like Ethereum’s Casper project studying questions of how to design a maximally useful and relevant proof of stake protocol for the next generation of cryptocurrencies.
Despite its potential shortfalls, we believe proof of stake represents a critical new development and direction in both the blockchain and distributed consensus fields. With this in mind, we set out to apply previous work by Rafael Pass (an IC3 member) and others, in which a model for analyzing and proving consistency, chain growth, and restrictions on adversarial chain impact for proof of work blockchains was developed.
To more accurately model the nature of blockchain distributed consensus, and the implication of network delays, we propose a new model for consensus called the sleepy model. This model more accurately mimics the operation and naturally captures the design of permissionless blockchains. In the sleepy model, a user (node or miner) can leave or join the protocol at will. This is modeled by (non-crashed) users in the protocol being given the ability to “sleep”, or go offline and rejoin the network at some unspecified later date with unmodified original state. The key question then becomes how can we design a useful consensus protocol in the sleepy model, when at least half of all online nodes (or stake) is honestly following the protocol?
The guarantees of consistency and availability are rigorously defined in this new model, more accurately capturing the guarantees users expect from blockchain protocols. The analogues of proof-of-work style guarantees like chain growth (availability) and chain quality (integrity) are also discussed. We believe this new class of consensus protocols in the “sleepy” model represents one of the fundamental contributions of blockchains to the distributed consensus space. Neither the asynchronous, partially synchronous, or synchronous models, in either a permissioned or permissionless setting, prove sufficient to model or reason about these new consensus protocols or the probabilistic and often economic guarantees they provide.
To that end, we are working on two protocols proven in the Sleepy model: Sleepy and Snow White.
Sleepy is a simple protocol intended to achieve the guarantees of chain quality, chain growth, and consistency/agreement with 51% of online nodes being honest. This protocol is intended for deployment in a permissioned context, and assumes stake assigned or instantiated by some trusted source. This makes Sleepy ideal for bankchains or other permissioned deployments, in which the set of stakeholders is known a priori but the blockchain guarantees of robust, auditable distributed consensus remain desirable. Every second, every member of the committee is eligible to “mine” a new block in the system, which involves a standard block mining solution with a public source of entropy as the nonce. Standard difficulty adjustments retarget the block interval to a desired target, as in Bitcoin and Ethereum today. The challenges of choosing an appropriate, ungameable mining function and source of entropy are tackled in the work, and proof is given that no committee member can manipulate the protocol to their advantage.
Snow White, on the other hand, is an extension of Sleepy intended to provide the same rigorous blockchain-derived guarantees in a permissionless setting, such as in the deployment of a public cryptocurrency. Obviously, this is substantially more difficult: choosing appropriate committee members for the block lottery, as well as ensuring that no coalition of these committee members (of bounded size) can game the protocol for more than a negligible advantage, are highly nontrivial. The resulting protocol is actually quite simple: each step, a committee mines as in Sleepy, with a shared source of entropy h0. With sufficiently many bits of entropy in h0 and an appropriately selected committee weighted on stake, it is possible to prove the desired result of chain quality, growth, and consistency in the Sleepy model. Choosing both the committee and h0 such that no adversary or non-majority coalition of adversaries gain substantial advantage by deviating from the protocol is the key to the construction and concrete parameters of the protocol, which are discussed further in our full publication.
Sleepy and Snow White represent the first rigorously justified and proven blockchain consensus protocols in both the permissioned and permissionless proof of stake space. It is our belief that the rigorous proofs of security are valuable as both theoretical efforts and to guide protocol development and deployment. Both the proof and concrete parameterization of these protocols are highly non obvious, and while heuristic protocols designed elsewhere in the community (with only informal justification) may operate in a similar manner to Sleepy, there is no guarantee that subtle network-level, timing, committee / stake poisoning, and other attacks are not present in these protocols. In our work, we assume an optimal adversary with ability to delay network messages up to some arbitrary time, a very strong notion of attacker that makes our protocols the most rigorous conceived in the space thusfar.
You can read about the papers in prepublication manuscripts we have uploaded for release on ePrint: Snow White, Sleepy. Further conference or journal publications with implementation details of these systems, full proofs, simulation results, and experimental comparisons to existing cryptocurrencies are currently in development. We hope to share more exciting news about these new protocols soon.
[It is worth noting that our willingness to assume that the majority of online coins are honestly following the protocol is an assumption that `has been challenged <https://blog.ethereum.org/2016/12/06/history-casper-chapter-1/>`_ by the Ethereum foundation. We do not necessarily agree with these criticisms or model; we believe that the ε-Nash equilibrium achievable in *Snow White is sufficient for the design of a robust, decentralized coin. Nonetheless, we believe developing and proving protocols secure in this context is valuable: both as the most natural model for private blockchain deployments, and to illuminate common pitfalls in proof of stake protocol design that may lead to attacks in naive protocols. We look forward to a full specification of Ethereum’s Casper, and to comparing both its assumptions and attack surface with that of Snow White.
There are many estimates of the electricity consumption of the Bitcoin network, but we don’t find them convincing. For example, this widely cited one derives an upper bound of 10 GW (in 2014!). As we’ll see from a simple calculation below, that would imply that miners were losing huge amounts of money. So here’s our crack at a crude estimate.
Using the technique in this paper, to obtain a lower bound on electricity consumption, let’s take the Antminer S9 to represent the state of the art in mining rigs. It consumes 0.098 W/GH. The current mining rate of the Bitcoin network is about 3,330,000 TH/s. Thus, were all miners using Antminer S9s, the electricity consumption of the network would be about 326 MW. (Of course, many miners are probably using less efficient rigs, so this is a loose lower bound.)
To obtain an upper bound on electricity consumption, assume that miners are rational, i.e., won’t mine if it causes them to lose money. At the current price of about $1000 / BTC, given a 12.5 BTC mining reward and block production rate of about 6 blocks per hour, the global mining reward per hour is about $72,500. A common, extremely cheap form of electricity used by miners is Chinese hydroelectric power; the very low end of the levelized cost of such electricity is $0.02 / kWh. Thus rational miners will consume no more than 3.625 GW of electricity. (Of course, this estimate disregards the capital costs of mining, and is therefore probably a quite loose upper bound.)
Taking the log-average of these two bounds yields an estimate of 1.075 GW, about the output of a single unit in a nuclear power station. Ireland’s average electricity consumption is about 3.25 GW (as derived from this 2013 figure).
Again, this is a crude estimate, but we believe it’s probably within a factor of 2 of the real one.
It is possible to outsource mining with the standard cryptocurrency PoW H(X,n) ≤ Z, simply by declaring a puzzlet to be the problem of finding an n such that H(X,n) ≤ Z_{easy}, for some Z_{easy} > Z. In other words, a worker can be asked to find a solution to a PoW easier than the target. But with some probability, a solution to H(X,n) ≤ Z_{easy} will also be a solution to H(X,n) ≤ Z, i.e., will solve the outsourcing miner’s PoW.
The problem with this approach is that a malicious worker can mount a block withholding attack. If it happens to find a solution to H(X,n) ≤ Z, it can simply not submit it. Or it can demand a bribe from the outsourcer. Use of rin and rout conceals from a worker whether or not a puzzlet solution is also a solution to the global PoW, preventing such attacks.
Quelle: The Greening of Blockchains
R3 is a financial innovation enterprise that aims to design and deliver distributed ledger technologies to global markets. They lead a consortium partnership of over 50 of the world’s top financial institutions. Through collaboration with their partner research centers, they’re working to test blockchain technologies and their applications towards developing a global financial-grade ledger.
Along with ten of its member banks, R3 has recently developed a proof-of-concept for a Know Your Customer (KYC) registry. KYC is about doing customer due diligence, and determining a valid identity. The systems currently in place are meant to catch identity theft, avoid fraud, prevent money laundering, and stop terrorist financing.
Over the course of three months, R3’s Lab and Research Center utilized blockchain technology to create a KYC registry that would satisfy regulatory requirements, as well as allow identities to be managed by their owners. According to a statement from R3, the project was able to simulate the establishing of the identity of both an individual, and a legal entity, including identity attestation by a third party. The transparency, and immutability of storing identification information in the blockchain seems like a logical choice for fighting illicit activities in the financial sector.
KYC is an important aspect of modern banking which would benefit from an overhaul. Long turnaround times and needlessly redundant processes have made for an inefficient current model. As costs rise, and the process continually grows in complexity, banks are beginning to struggle with their customer on-boarding process. A study by Reuters showed some financial institutions were spending upwards of $500-million annually in relation to KYC compliance. CEO of R3, David Rutter, said:
„The growing complexity and cost of KYC compliance requirements presents a major challenge for banks on-boarding new clients and is having a negative impact on those client relationships. Distributed ledger technology can provide a unified view of clients whilst also significantly reducing costs and time spent verifying identity.“
If R3’s platform were to be deployed, participants would be able to create their own identities, and link them to any relevant documentation. What’s great is an individual would manage their own identity, and simply permission access to their ID when necessary. In this system, a company could request additional validation through authoritative participants to attest to an ID. This means only those who need access to your data will be able to see it, because you specifically enabled that access.
This idea is similar to how distributed ledgers would revolutionize the healthcare industry, particularly in regard to the storage of medical history on a blockchain. With the implementation of R3’s KYC registry it would enable a customer to have one global ID, completely in their control. This increases security for the individual, and increases cost-efficiency for financial institutions.
Quelle: R3 Uses Blockchain To Streamline KYC For Banks Around The World

Money sent to Myanmar instantly with Everex’s Ethereum-based mobile payments app
Over 100 migrant workers transferred money instantly over blockchain to their homes in Myanmar in the last months. It marks a successful pilot test for Everex, a company aiming to give financial access to the world’s huge “Bottom of the Pyramid” (BOP) population. Overall, average transaction took less than a minute and recorded savings of over 7% in remittance cost and currency exchange rates. Everex essentially hands the power to send any amount of money fast and cheap around the world to individual users, wherever they live.
The test is just a small start, but has major significance.
Over 850,000 Thai baht (around $24,000 USD) were transferred using the Everex wallet, a mobile and web based app that sends digitized national currencies using Ethereum blockchain.
With over 500 signed users, mainly in Thailand, the Everex wallet is capable of transferring any custom digital asset over the Ethereum blockchain.
Sending and currency conversion both happened in less than a minute and incurred no transaction fees.
Although the test recipients used Myanmar money-changers to switch from CryptoCash back to physical cash, no centralized entity performed the actual remittance. This cuts time and costs dramatically, since the transmission process was automated with programmable smart contracts on Ethereum.
This means powerful financial tools, which have always been the proprietary domain of large financial institutions, are now available to ordinary people everywhere.
Everex understands the value of national currencies and existing financial networks. Unlike some blockchain projects, it’s not trying to replace them completely — the aim is to make them better.
In this world, there’s still an important role for banks and other financial players to store the “real money” that backs up “CryptoCash” and to keep its value stable.
Estimates say there are between two and five million Myanmar citizens now living in Thailand.
In fact, it’s possible as much as 10% of the country’s 51 million population lives overseas — though the exact number is uncertain. The largest number lives in Thailand, with the rest spread throughout the rest of Asia.
This Economist article of two years ago highlights how mistrust in existing remittance and financial networks meant Myanmar workers sent most of their money home via informal channels.
A trust-based cash system called hundi — similar to the hawala remittance networks of the Islamic world — served their needs. These systems have little transparency and often hide a mountain of extra charges in unfavorable FX rates and conversions, even if rates appear low on the surface.
But the story highlights how, if people cannot use or trust existing financial systems, they’ll find a way to route around them. That’s where Everex comes in — transparent and requiring far fewer human intermediaries.
Everex offers the best of all these worlds. Transfers and conversions are based on the global Ethereum smart contracts network — utilizing the latest in blockchain technology.
Quelle: Over 100 Migrant Workers Test Blockchain Remittance in Thailand – Everex
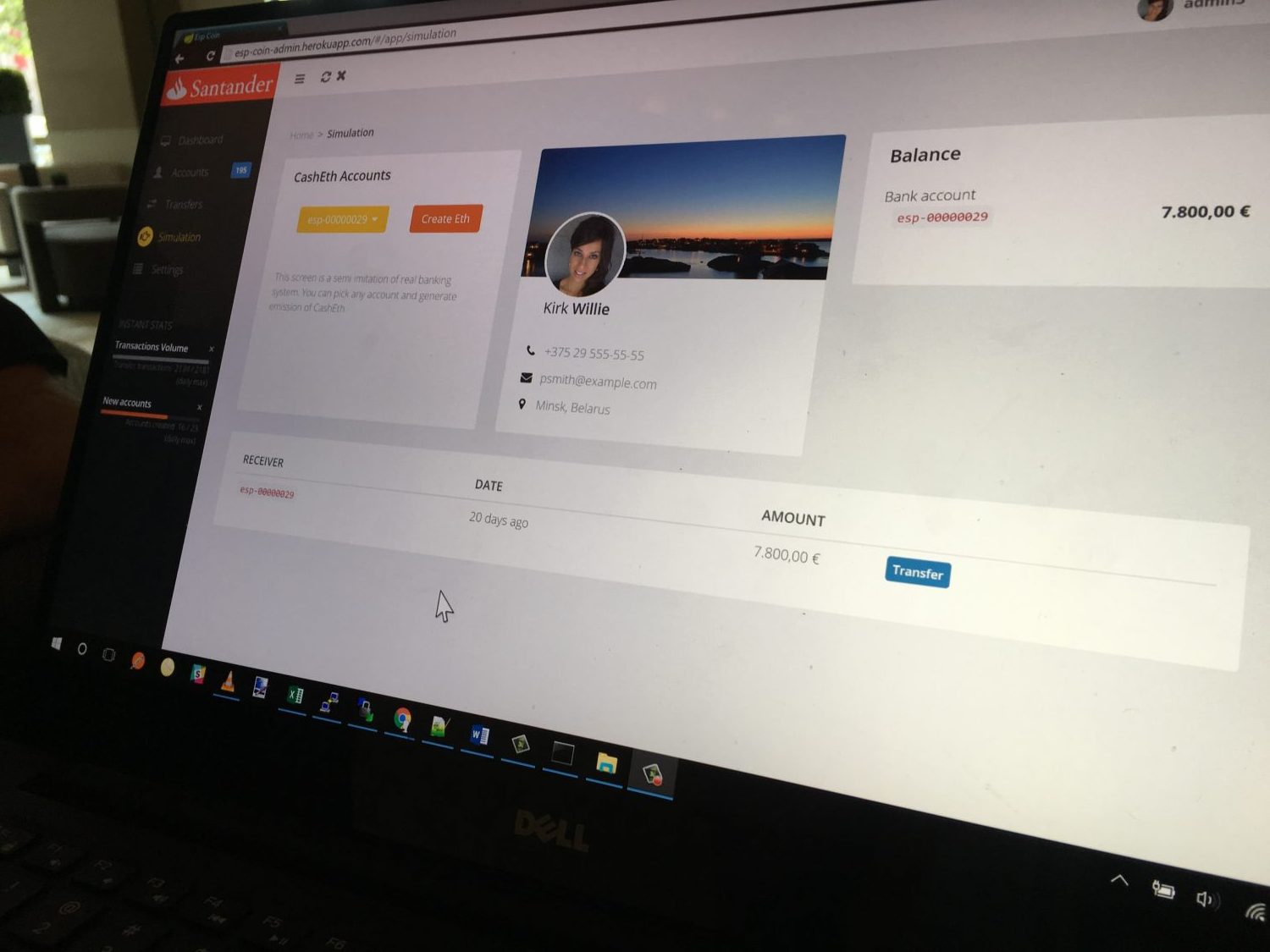 Spanish banking giant Santander is working on a project that explores how it could digitize customer cash using the public ethereum blockchain.
Spanish banking giant Santander is working on a project that explores how it could digitize customer cash using the public ethereum blockchain.
Revealed today during a panel talk at Devcon2 by Ether.camp founder and ethereum Java client developer Roman Mandeleil, the news was confirmed by representatives of Santander. In statements, Santander said its goal is to open up its bank-issued funds to a community of innovators as a way of tapping additional efficiencies.
“I saw everything to do with either government regulation or corporate control as just being plain evil. And I assumed that people in those institutions were kind of like Mr. Burns, sitting behind their desks saying, ‘Excellent. How can I screw a thousand people over this time.’”
In this way, his worldview was harmonious with the vast majority of Bitcoin early adopters who fully expected the technology to operate as a stealthy foil for the status quo. And though he says he has substantially updated his binary assessment of good and evil, Buterin is still motivated by a conviction that the powerful have far too much power.
Im Silicon Valley dürften einige Risikoinvestoren gerade nervös werden. Ihr Geschäftsmodell wird gerade disrupted. Normalerweise läuft das folgendermaßen: Ein paar aufgeregte Jungunternehmer legen ihnen zitternd einen Businessplan vor, wie sie Firmen oder ganze Branchen durch eine Softwarelösung ersetzen wollen. So wie Amazon es mit Buchläden gemacht hat, Airbnb mit Hotels und Uber mit Taxidiensten.
Sind die Investoren überzeugt, sagen sie, die Branche sei reif für die Disruption und geben ihr Geld gegen Geschäftsanteile am Start-up. Läuft dann alles wie geplant, sind die Firmenanteile der Investoren irgendwann wahnsinnig viel wert – während anderswo Leute auf der Straße stehen, weil ihre Jobs durch eine App ersetzt wurden.
Eigentlich wäre das auch der Weg gewesen für die Brüder Christoph und Simon Jentzsch, zwei Programmierer aus der kleinen Universitätsstadt Mittweida in Mittelsachsen. Zusammen mit ihrem Londoner Partner, dem Fintech-Unternehmer Stephan Tual, bauen sie derzeit die Firma Slock.it auf. Slock.it soll eine Plattform für das Internet der Dinge werden, eine Art Airbnb für alles, mit dem sich im kommenden Zeitalter der totalen Vernetzung die ungenutzten Potenziale leerstehender Parkplätze, ungefahrener Autos oder ungenutzter Rechenkapazitäten vermarkten ließen. Die Universal-Sharing-Plattform.
„Ich finde es nicht richtig, wie stark eine Handvoll Investoren die Entwicklung der Technologie bestimmt“, sagt der 31-jährige Christoph Jentzsch. Jede starke Zentralisierung von Entscheidungsprozessen widerspreche seiner politischen Haltung. Also hätten er und seine Partner einfach eine Bauanleitung für eine vollelektronische, dezentrale Investmentfirma verfasst und online gestellt, als „ein soziales Experiment“. Sie heißt DAO – Decentralized Autonomous Organisation.
Dabei hatten sich die drei ein Konzept der Wirtschaftstheorie zunutze gemacht, die Vertragstheorie. Laut der ist eine Firma nichts anderes als ein Netzwerk aus Verträgen, in denen Ziele, Befugnisse und Zeiträume definiert werden. Alles innerhalb der Firma wird durch sie gelenkt, von unten nach oben, ob Maschine oder Mensch. Jeder kennt Arbeitsverträge, die das Handeln der Mitarbeiter steuern sollen. Angestellte „exekutieren“ vertraglich vorgegebene Aufgaben. Daher auch der englische Titel CEO – Chief Executive Officer.
Aus der Sicht von Programmierern lässt sich das meist relativ einfach als Programm formulieren, als eine Reihe von elektronischen Wenn-dann-Beziehungen. Smart Contracts heißen solche sich automatisch ausführenden Digitalverträge. In der Theorie sind sie objektiver als Manager, die gerne mal ihre eigenen Interessen über Firmenvorgaben stellen.
Im Fall der DAO ersannen die Slock.it-Gründer ein einfaches Prinzip: Zuerst können sich Interessierte in die Firma einkaufen, indem sie elektronische Token erwerben. So kommt Geld auf das Firmenkonto, also den Fonds. Die Token wiederum repräsentieren Stimmrechte. Nach einer vierwöchigen Tokenauktion zum erstmaligen Geldsammeln kann der digitale Investmentfonds entscheiden, wohin mit dem gesammelten Geld. Das bestimmen die Besitzer der Stimmrechte – in einer elektronischen Abstimmung, ähnlich dem E-Voting. Die DAO ist also im Kern eine Geldsammelmaschine plus Entscheidungsgremium.
Der große Unterschied zu einem normalen Investmentfonds aber ist nicht nur, dass hier anstelle von CEOs und Managern eine Art elektronische Aktionärsversammlung – auch wenn sich Christoph Jentzsch gegen dieses Wort wehrt – entscheidet, sondern vor allem, dass die Firma keinen physischen Sitz hat.
Ihre Adresse lautet: 0xbb9bc244d798123fde783fcc1c72d3bb8c189413.
Getreu der Dezentralisierungsphilosophie der Jentzsch-Brüder ist das Investmentfirma-Programm in einer neuen Form von Peer-to-Peer-Netzwerk abgespeichert, der Ethereum-Blockchain. Das Prinzip ist von Bitcoin bekannt: Es handelt sich schlicht um ein gewaltiges Register, das wie das Kontobuch einer Bank oder ein großes Excel-Dokument automatisch alle Aktionen seiner Nutzer verzeichnet. Während es bei der Bitcoin-Blockchain um die Überweisungen von digitalem Geld geht, die jeder angeschlossene Rechner aufzeichnet, damit niemand betrügen kann, hat Ethereum den Handlungsspielraum erweitert. Die Ethereum-Blockchain ist dafür geschaffen, dezentral komplexe Handlungen auszuführen. Richtige Programme. Beispielsweise die Vertragsprogramme, aus denen die DAO besteht. Die Ethereum-Währung Ether dient hierbei als eine Art Lastwagen für Informationspakete.
Der Vorteil jeder Blockchain: Sie ist äußerst hartnäckig. Fällt ein Rechner aus, führen Tausende oder sogar Millionen andere weltweit die Arbeit fort. Um Programme oder auch Geld im Netzwerk zu verorten, werden Zahlen- und Buchstabencodes wie jener der DAO erstellt. Sie dienen als anonyme Nummernkonten.
Sinnigerweise kann man sich in die neue Investmentfirma nur mit der Digitalwährung Ether einkaufen, die auf anonymen Nummernkonten basiert. So ist also nicht sofort erkennbar, wer genau die Investoren sind. Totale Transparenz plus totale Anonymität, das versuchen die Blockchain-Jünger zu vereinbaren. Wobei die erfolgreichen Ermittlungen gegen Geldwäscher, die ihre Spuren mit noch so verschachtelten Bitcoin-Überweisungen verwischen wollten, allen Anonymitätssuchenden eine Warnung sein sollten.
Und aus Sicht von Staaten und Steuerbehörden sind die legendären Briefkastenfirmen in Panama im Vergleich mit der DAO so retro wie ein Grammophon zu Soundcloud.
Zumindest in der Theorie der Entwickler haben nicht nur Staaten keinen Zugriff auf die neue Firma, falls man sie überhaupt so nennen kann. Möglicherweise kann überhaupt niemand sie stoppen. Darauf ist Jentzsch stolz. The DAO sei nicht nur dezentral, sondern eben „autonom“. Der Code lege fest, dass es keinen Chef gebe: „Niemand ist in der Lage, der Organisation den Stecker zu ziehen und ihren Betrieb einzustellen“. Nicht einmal die Erschaffer selbst. „Nur wenn alle Token-Inhaber einstimmig entscheiden, den Betrieb einzustellen, wird die DAO geschlossen.“ Im Falle einer größeren Uneinigkeit in der Versammlung der Stimmrechtsinhaber würden automatisiert Abspaltungen erzeugt – und so entstünden ähnlich einer Zellteilung neue DAOs, gefüllt mit dem Geld der abtrünnigen Subgruppen.
Damit könnten die Sachsen einem langgehegten Traum der Blockchain-Gemeinde aus radikal-libertären, staatskritischen Codern zum Durchbruch verhelfen. Dem Traum von der Verselbstständigung des Kapitalismus. Klassisches Beispiel: Selbstfahrende Taxis, die sich selbst gehören und Reparaturen oder sogar Expansion durch ihre Erlöse finanzieren. Inspiriert ist das ganze durch Ethereum-Vordenker Vitalik Buterin. Er sagt, ihn habe der Science-Fiction-Roman Daemon des US-Bestseller-Autoren Daniel Suarez beeinflusst, in dem eine dezentral abgespeicherte Roboterfirma beschrieben wird, geführt von einer künstlichen Intelligenz: Daemon.
In der DAO entscheiden allerdings Menschen. Der Firma können auf elektronischem Weg Vorschläge zur Finanzierung von realen Firmen oder auch gemeinnützigen Organisationen zugesandt werden. Diese werden von menschlichen „Kuratoren“, darunter einige der wichtigsten Ethereum-Entwickler, kurz auf formale Korrektheit geprüft. Dann werden sie in einem mindestens zweiwöchigen Abstimmungsvorgang allen Stimmrechtsinhabern vorgelegt. Real auszahlend ist eine Schweizer Firma in Neuenburg, geführt von einem Schweizer Piraten-Politiker.
Slock.it-Berater und Ethereum-Blockchain-Mitentwickler Gavin Wood erwartet, dass sich bei den Abstimmungen eine Art Parlament bilden könnte, mit Parteien und Gruppierungen. „Je nachdem wie man es ansieht, ist die DAO nicht eine Firma, sondern ein Staat.“ Schon in seinem Konzeptpapier verweist Christoph Jentzsch auf die Liquid-Democracy-Technik der Piratenpartei. Allerdings wäre die DAO eine Demokratie, in der man um so mehr Stimmen hat, je vermögender man ist.
Ob das alles legal ist, ist umstritten. Vor allem: legal nach welchen nationalen Gesetzen eigentlich? Das ganze existiert ja nur im Netz und nicht einmal auf einem einzelnen, lokalisierbaren Server. Und wie gut oder böse die DAO im Verhältnis zu den bisherigen Silicon-Valley-Investoren ist, wird abhängen von ihren Investitionen.
Wenn die DAO-Stimmberechtigten sich dafür entscheiden würden in nordkoreanische Zwangsarbeiterfabriken zu investieren – wer könnte sie stoppen? Jentzsch sagt, die rechtliche Haftbarkeit könne auf der Input-Seite liegen, also bei den Geldgebern und Abstimmenden. Allerdings seien die Rechtsanwälte, die er kontaktiert habe, meist überfordert gewesen mit der neuen Situation. In der traditionell nicht gerade staatsverliebten Finanzbranche wartet man bereits auf das wütende Aufschnauben der Regulatoren.
Andererseits haben die Slock.it-Gründer wohl nun ihren perfekten Investor gefunden. Sie haben der DAO als Allererste einen Vorschlag vorgelegt, der wohl durchkommen dürfte. Und da die DAO ja einfach nur Geld vorschießt und im Gegenzug dafür wohl Profitanteile kassiert, wäre es technisch auch denkbar, dass sie neben der Rolle als Anschubfinanziererin auch als zahlungskräftige Kundin von Slock.it tätig werden könnte.
Auf jeden Fall ist das ganze eine Fintech-Revolution. In einer Zeit, in der viele über das angeblich nahende Ende des Kapitalismus reden und über den Post-Kapitalismus, erfinden andere den Kapitalismus neu: als digital entfesselte Spekulations-Maschine.
Bis zum kommenden Samstag läuft die große DAO-Geldsammelaktion noch. Danach nimmt die Firma ihren Betrieb auf.
Quelle: Zeit online
Ethereum is a contract validating and enforcing system based on a distributed public ledger (or blockchain) such as the one implemented by the Bitcoin cryptocurrency. Yet, Ethereum also features an internal Turing-complete scripting language that can be used to encode advanced transaction types directly into the blockchain. This allows for the deployment of self-enforcing smart contracts (such as joint savings accounts, financial exchange markets, or even trust funds) as well as distributed autonomous organizations (DAOs) that subsist independently of any moral or legal entity. These algorithmical entities are both autonomous and self-sufficient: they charge users from the services they provide so as to pay others for the resources they need (e.g. bandwidth, cpu). Thus, once they have been created and deployed onto the blockchain, they no longer need (nor heed) their creators.
But if DAOs are independently operated — neither owned nor controlled by any given entity — who is actually in charge, responsible for, or accountable for their operations? And if their resources cannot be seized (because DAOs have full sovereignty over them), how can they be required to pay damages for their torts? This talk will analyse the interplay between distributed autonomous organizations and the law, with a view to explore the dangers and opportunities of Ethereum: could this new platform promote the establishment of an entirely decentralized society, or will its disruptive potential eventually be absorbed by the established system?
Primavera De Filippi is a postdoctoral researcher at the CERSA / CNRS / Université Paris II (Panthéon-Assas). She is currently a research fellow at the Berkman Center for Internet & Society at Harvard Law School, where she is analyzing the challenges raised by distributed architectures and multimedia applications in the context of cloud computing and peer-to-peer networks.
Source: https://cyber.law.harvard.edu/events/luncheon/2014/04/difilippi

Ethereum, the decentralized application and smart contracting platform prepares to shoot the starting gun, as their Frontier release reaches 99% 98% completion. Miners, who have been waiting a year since the crowdfund, have begun sharpening their GPU pick axes.
[Update: Another bug seems to have been added over night, bringing it back to 98%]
Imagine a day when you want to go meet some friends for a drink. You pull out your iPhone 13, open the decentralized uber app, and using your preferred cryptocurrency, you pay for a smart cab.
The vehicle has no steering wheel. It does not need one. Artificially intelligent driving software issues an offer to pick you up, competing with 50 other smart cabs in the area. The best deal locks in on the blockchain exchange and a few seconds later the cab arrives, ready to facilitate and enhance the rest of your night out.
The door closes behind you as you walk onto your front lawn. The door can only be opened by those with a specific crypto token, which like Bitcoin, can be transferred to your family or friends, as you see fit.
From the inside, it looks more like a club lounge than a taxi, very much like high-end limousines look and feel today, except in the size of a 4-door sedan. Since smart cars virtually never crash, you don’t really need a seat belt, and all chairs are facing the center of the vehicle. You are served a cocktail to get you started as you journey to the restaurant.
Everything in your home, from your toaster to your washing machine, can be controlled digitally and from anywhere in the world. You remember, as you drive to the gathering, that you forgot to start the dryer. No problem, there’s an app for that too. Just approve the right micro transaction on the blockchain with a voice command to your smartwatch.
This future is not hard to imagine. This is only a small glimpse of everything being made possible by technologists today, and the blockchain promises to deliver an essential piece of security and simplicity to the rising Internet of Things.
To some this might seem like a dream land, a place where agreements are completely peer to peer, enforced by mathematics, not by law, nor corruptible human bureaucracies and our biases.
To others, the knowledge that is hard-earned through the daunting insecurities of technology systems and through ubiquitous and scandalous hacks could spell disaster for such a world, especially should control of all human tools be hijacked by malicious actors. The security of our information systems is, therefore, of utmost importance, since this future is near. The Internet of Things at this scale is a reality waiting to happen. The question is, will it be secure?
Well, as far as security in the Age of Information goes, blockchains are very promising. Bitcoin has proven that decentralized networks can hold massive amounts of value. While individual parties may be hackable, such as the graveyard of centralized Bitcoin exchanges and wallets, still the protocol remains whole, and the economy vibrant and growing.
Ethereum is among such blockchain technologies, and it is believed by many to be one of the most promising and anticipated decentralized smart contracting protocols in development today.
Its vision, brought to us by distributed consensus engineer and visionary, Vitalik Buterin, is about to take its first step out of a two-year development cycle that has up until now been confined to test networks.
It will go down in history as having been one of the most successful crowdfunded projects hands down, having raised over US$18 million in September 2014. As of today, it sits in third place as having raised the most money among crowdfunded projects, ever.
Ethereum, of course, is not only being developed by Buterin. The Ethereum community is as international and decentralized as its protocol, composed of hundreds of volunteers and a large operations and development team. It includes Gavin Woods, Stephen Tual, Jeffrey Wilcke and many more. And they are building on the work of many before them, as we all are.
In fact, the term ‚smart contract‚ dates back to 1993, credited to pioneer Nick Szabo.
“Frontier” is the name of the first release of the Ethereum main chain, and it is called that for a reason, as illustrated by a documentation on the release, which states:
“The Frontier is the first live release of the Ethereum network. As such you are entering uncharted territory and you are invited to test the grounds and explore. There is a lot of danger, there may still be undiscovered traps, there may be ravaging bands of pirates waiting to attack you, but there also is vast room for opportunities.”
The document goes on to warn that Frontier is a command-line-heavy release. Those hoping for an easy-to-use interface are advised to “step back, watch from a distance for a while and wait until more user friendly tools are made available,” although there are some user interfaces in development, such as Mist and AlethZero.
This, however, should not discourage miners and tech-savvy entrepreneurs looking for the next gold rush. If there was ever a hot coin to mine, it might be this one.
While there is no official launch date yet — and I would not hold my breath for a “Heads up, we are launching Thursday” — there has been recent speculation that Frontier will launch within the next two weeks or so.
One obvious reason is the milestone barometer that follows the progress of the Frontier release. It was at 98% earlier this July. Now it sits at 99% 98%.
Stephen Tual also made a post on July 15 in which he suggests that the release is very close. Here are two clues he left:
“We’re very happy with the way Olympic [the Frontier testnet pre-release] took shape, so much so that many of the Frontier gotchas (chain reset at Homestead, 10% mining rewards, checkpointing) were deemed unnecessary.”
“Eight days ago we entered feature freeze. Meaning we are focusing exclusively on fixing bugs in the Geth codebase right now, we’re not adding new features anymore.”
Fairlay’s prediction market is also betting on whether “Ethereum frontier goes live before August,” with 113 votes and a roughly a 20% weight towards yes. Participants also seem very confident Frontier will launch before September. [Update: Prediction markets seem to also have shifted over night, this is an updated image]
Ethereum will use a mixed approach to their security protocol, starting off with a miming phase to distribute the ether units of account and then shift towards a proof of stake algorithm. Though details as to exactly when also seem to be scarce and in development.
Tual points out that there is still a “lot of admin processes to deal with: [ensuring] we have a strategy to recover from forks, a well rounded helpdesk, etc.” He adds that, “Once we are happy that Frontier is ‚done‘ and that the aforementioned processes are in place, we’ll publish a blog post explaining the next steps. We still won’t give a date, but at that point miners will want to be sure to be ready.”
Which brings us to mining.
— RC2 mining rig, “‘Olympic‘ edition,” named after the last proof-of-concept Ethereum test release
Tual has published a very detailed “How to Mine Ether” guide and FAQ, where he also describes a GUI for miners called EthMiner. It uses its own algorithm called “EtHash” a “Hashimoto / Dagger hybrid.”
I asked on r/ethereum, “What are my chances of actually mining any Ether on Frontier release, and how would I do it?” I received one particularly insightful response from redditor “playingethereum,” who said:
“The chances are incredibly good if you own a GPU with greater than 1 GB of video memory. You’ll need to set up your miner in advance. Ethereum has a very fast block time (12 seconds), so lots of people will find a couple blocks. The trade off is that the value of the blocks is significantly less than you would expect with bitcoin. For example, a current bitcoin block is worth ($300 * 25 bitcoin) = $7500, while an Ethereum block might be worth about ($3 * 5 ether) = $15.00.”
Keep an eye out for updates on those numbers.
Some of the popular and anticipated projects waiting for Ethereum to launch include:
Though there are plenty of projects being developed on the sidelines of Ethereum and there’s likely some buried, undiscovered gems, most of them preparing and waiting for the starting gun. Boom.
Source: http://cointelegraph.com/news/114898/ethereum-prepares-for-take-off
So I’m not sure if this kind of development methodology has ever been applied to such an extreme before so I figured I’d document it. In a nutshell, it’s sort of like test-driven triplet-programming development.
While speed-developing our alpha codebase, four of us sat around a table in the office in Berlin. Three people (Vitalik, Jeff and me) each coders of their own clean-room implementation of the Ethereum protocol. The fourth was Christoph, our master of testing.
Our target was to have three fully compatible implementations as well as an unambiguous specification by the end of three days of substantial development. Over distance, this process normally takes a few weeks.
This time we needed to expedite it; our process was quite simple. First we discuss the various consensus-breaking changes and formally describe them as best we can. Then, individually we each crack on coding up the changes simultaneously, popping our heads up about possible clarifications to the specifications as needed. Meanwhile, Christoph devises and codes tests, populating the results either manually or with the farthest-ahead of the implementations (C++, generally :-P).
After a milestone’s worth of changes are coded up and the tests written, each clean-room implementation is tested against the common test data that Christoph compiled. Where issues are found, we debug in a group. So far, this has proved to be an effective way of producing well-tested code quickly, and perhaps more importantly, in delivering clear unambiguous formal specifications.
Are there any more examples of such techniques taken to the extreme?
The post The Ethereum Development Process appeared first on .